Yesterday RSM released the latest version of its open source Phishing Campaign toolkit, King Phisher. This new release includes some very exciting new features. One of the two primary new features is the addition of auto-completion for the Jinja and basic HTML tags in the message editor. King Phisher supports a large number of template variables on top of the ones built into Jinja. If you’re a regular War Room reader, you may have seen this coming, as we released a post outlining the details of our implementation using GTK and Python. The end result is what we hope will make writing templates faster and easier with fewer mistakes relating to the Jinja variables and less trips back and forth to the documentation.
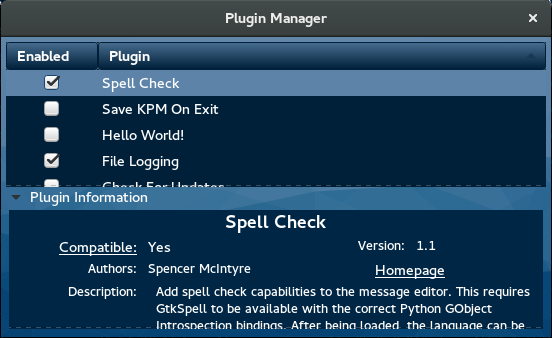
Additionally, the 1.3 release also includes the ability to load additional functionality in the form of plugins. As of the time of this writing, six plugins are available from the very basic “Hello World” (which serves as a simple demonstration) to the more complicated anonymous data collection plugin (which we’ll get to in a minute). Plugins can be loaded from the client interface and then need only be enabled. To help facilitate the distribution of plugins a new repository has been created to collect them. Installing a plugin from this repository is as simple as downloading the plugin and dropping it in a “plugins” subdirectory within the user’s data directory (typically $HOME/.config/king-phisher/plugins). Users interested in developing their own plugin will want to look through the developers documentation.
It is RSM’s goal to work with the King Phisher community to analyze the effectiveness of social engineering campaigns and user awareness programs. To that end, one of the first large plugins we’ve made available will gather anonimized results data that can be sent to RSM. Later this year, all of the gathered data will be included in a report that will be freely distributed to the community. We’re excited to be starting this initiative and hope to see users opt-in to collaborating. All that is necessary to participate is to enable the “Anonymous Data Collection” plugin. When run, this plugin will generate a JSON file which contains the count of various aspects of the campaign such as the number of messages sent, visits received etc. The file can then be sent to RSM. We respect our users privacy and understand the sensitive nature of the data collected by King Phisher and to that end, users are encouraged to view the file prior to sending it. We thank everyone for their involvement with our research efforts.
As a final note, future releases of King Phisher will start to more heavily target Python 3. With the latest versions of Ubuntu and Fedora being prime examples, many Linux distributions are starting to default to Python 3 over 2.7. King Phisher has supported Python 3.x for some time now, but with the next couple of releases users will start to be encouraged to transition over. A wiki page with instructions on how to switch from 2.7 to 3.x has been created and will slowly be updated with more details. Additionally, the next release will mark the first in which Python 3 is the default version that King Phisher is installed with when using the included installation script.
As always the latest release can be found on the projects GitHub page. Happy Phishing!
